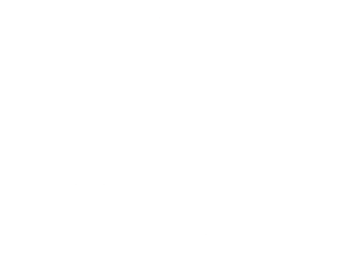
How to Eliminate Motor Speed Jitter Using Hysteresis Logic with Unlock Conditions
Problem Statement In motor control systems where speed is derived from an analog input (such as a potentiometer), small fluctuations in the input signal can cause frequent and unwanted speed changes. This leads to: Speed jitter Unstable user experience Excessive control updates Mechanical stress due to rapid small adjustments To address this, hysteresis logic […]
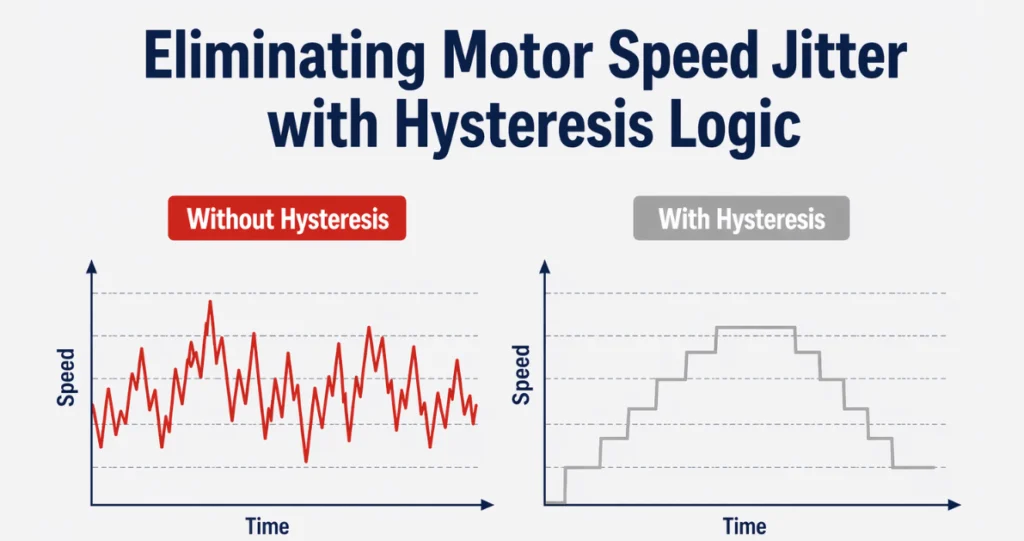
When Parallel Reception of GNSS and LTE in Modules Is Important
Source: learn.sparkfun.com In LTE + GNSS modules, the real engineering challenge is not simply integrating two radios. The true difficulty is enabling continuous GNSS reception while LTE transmission and reception are occurring simultaneously. This is what “parallel reception” really means in practice: Maintaining uninterrupted GNSS satellite signal reception during active LTE operation. Whether you need […]
Why Matter Protocol is The Future of IoT Connectivity

Credit: CSA Matter Brand Kit Introduction The Internet of Things (IoT) is transforming how we use and control various devices in everyday life. IoT is expanding into nearly every sector from smart homes and connected cars to industrial automation, healthcare, and smart cities. More companies are entering the market with their own devices and […]
How to Check RED Cyber DA Compliance: Free Gap Analysis Checklist

Since 1 August 2025, the RED Cybersecurity Delegated Act (Cyber DA) has been mandatory for all wireless-connected devices sold in the EU. If your product is not compliant, it cannot be CE marked and therefore cannot be legally placed on the EU market. For managers and technical managers, the challenge is clear: ensure that […]
EN 18031 Explained: EU IoT Security Standard for RED
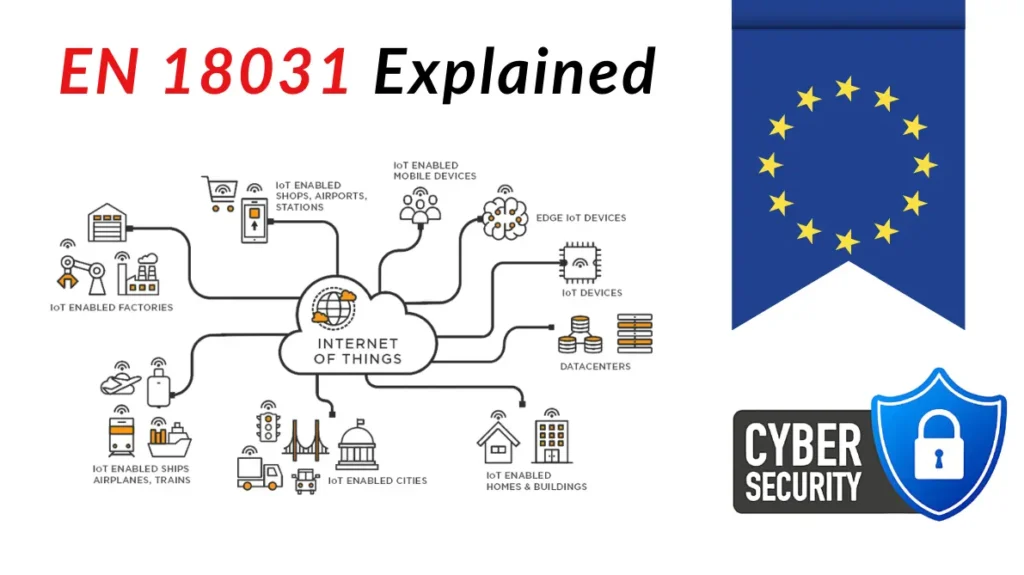
EN 18031 Explained: Meeting EU Security Standards for IoT Devices Wireless products that connect to the internet, handle personal data, or handle monetary value must meet the RED cybersecurity requirements. This comes from Delegated Regulation (EU) 2022/30 and its amendment that moved the due date to 1 August 2025. The EN 18031 series is […]
A Step-by-Step Guide to Comply With the EU RED Cyber DA (for Hardware Manufacturers)
As of 1 August 2025, the RED Cybersecurity Delegated Act (Cyber DA) is in effect . This means all wireless products sold in the European Union must now meet mandatory cybersecurity requirements. For hardware manufacturers, it’s a market access issue. Without compliance, your products cannot legally be sold in the EU. This guide walks […]
How to Comply an Existing IoT Device With RED Cyber DA Without Redesigning Hardware

The EU’s RED Cybersecurity Delegated Act (2022/30) comes into force in August 2025, making cybersecurity compliance mandatory for all internet-connected radio devices sold in the EU. This includes WiFi, BLE, and cellular-enabled devices, even if they are already CE-marked. At Oxeltech, we provide RED Cybersecurity compliance support for connected devices. Many clients ask: Do […]
What Every IoT Manufacturer Selling in EU Must Know About RED Cyber 2025
From 1 August 2025, the EU’s Radio Equipment Directive (RED) will enforce mandatory cybersecurity requirements for all internet-connected radio devices. This change affects nearly every manufacturer selling connected products, including those using WiFi, Bluetooth, or cellular technologies. What’s Changing? The RED Delegated Regulation (EU) 2022/30 activates Articles 3(3)(d), (e), and (f) of the directive. […]
SoC vs. SoM in Low-Power Devices
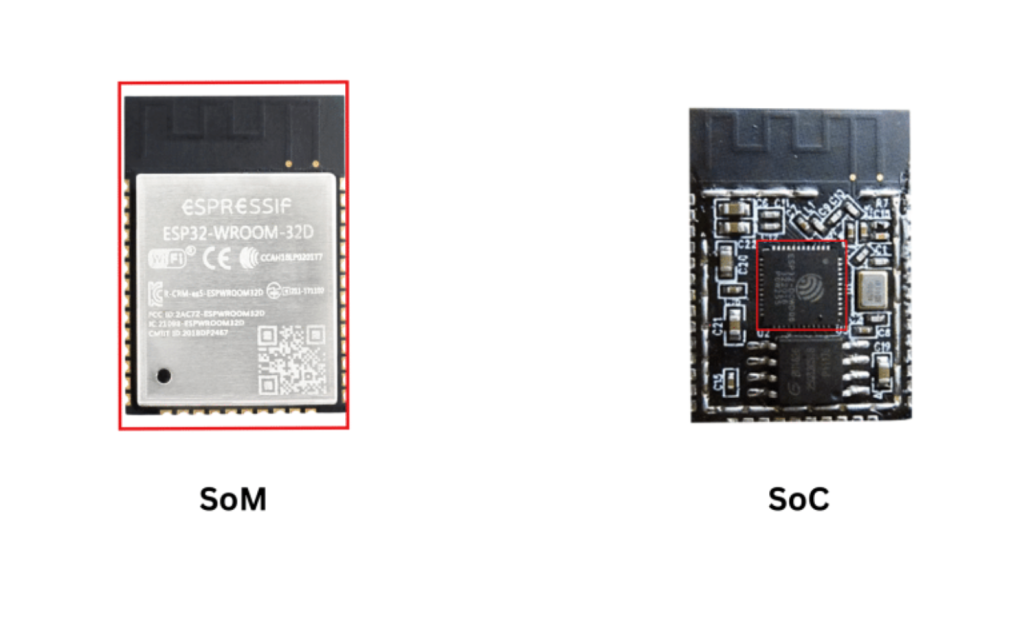
A SoC is a single chip that integrates key functions but requires external components, while a SoM is a ready-to-use module that includes a SoC plus supporting circuitry like power, memory, and RF, simplifying integration. The decision which one to use is a trade-off between full control (SoC) and faster deployment with lower RF risk […]
Coredump Can Help You with Embedded Firmware Debugging (Better than Breakpoints)

Source: embeddedcomputing Coredump captures the crash moment of an embedded system. It shows memory, registers, and stack traces. Firmware bugs are tricky. Hardware-software interactions are complex, resources are constrained, and runtime behavior can sometimes be unpredictable. For teams working on developing embedded products, this can feel like navigating in the dark. To reach the core […]